To follow up on our post last Friday, I was contacted by the author of the DarkComet RAT Trojan. He seemed quite upset that I suggested the new Mac OS X Trojan BlackHole RAT was related to his Windows creation.
Fabrication custom built frames by Mac's Ratz of Adel, Iowa. Mac's Hot Rod V8 Trikes! For more information and kit prices. FOR SALE V8 Trike SBC Chopper Springer SBC $8,900.00. FOR SALE 1929 Model A Sedan just finished Super, Super nice car Call for Price. FOR SALE 1937 Ford Rat Rod Frame Kit - Box Kit Combo $3,392.00. Future project truck. The real threat behind the software is this: The malware is shipped with genuine Apple code-signing signatures. This means the author of Proton RAT somehow got through the rigorous filtration process Apple places on MAC OS developers of third-party software, and obtained genuine certifications for.
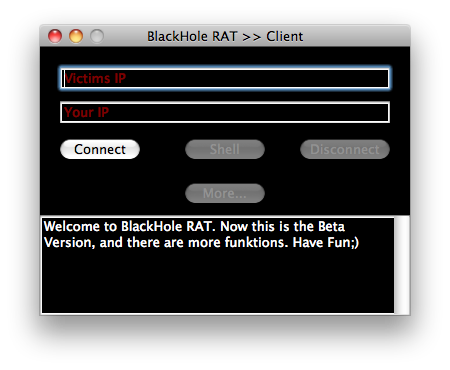
While the BlackHole RAT Trojan seems to be copying the behavior of DarkComet, the lack of functionality and the unsophisticated user interface clearly offended the author, who felt it was necessary to set the record straight.
- News: Deadly Lungworm Parasite Spread by Rats & Snails Is More Prevalent Than We Thought How To: Get the Public Beta Preview of Mac OS X 10.11 El Capitan How To: Dual Boot Mac OS X 10.11 El Capitan & 10.10 Yosemite How To: Download OS X 10.11 El Capitan on Your Mac.
- XAgentOSX is a piece of malicious software that is specifically designed to target Mac users. The program acts as a RAT (remote access trojan) that can be very destructive. Being a RAT virus, the malware is able to allow the remote access to the threat actors behind it, so as to control the target device and possibly execute malicious tasks.
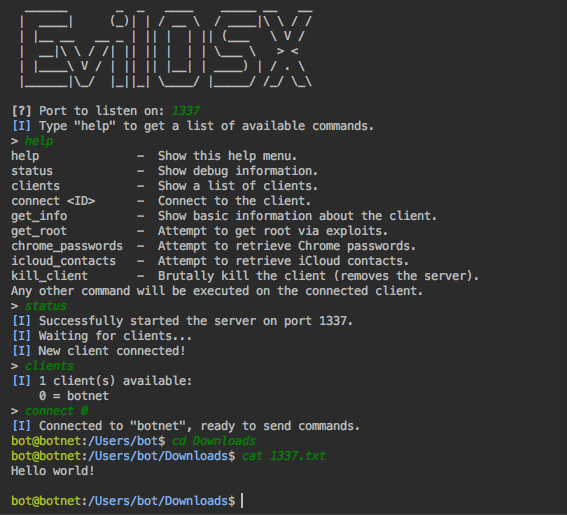
To make a point, DarkComet’s author acknowledges that he is developing his own Mac OS X Trojan, called DarkCometX, that is not yet finished. He provided the following screenshot.
Learning of two Mac OS X Trojans in less than a week was, admittedly, a bit of a surprise. Technically, in and of itself, writing a Trojan is not illegal. It’s all in what you do with it.
Looking at the code and descriptions, though, I think it is clear what the authors expect you to do with their “products.”
BlackHole RAT includes text saying things like
'I am a Trojan Horse, so i have infected your Mac Computer. I know, most people think Macs can't be infected, but look, you ARE Infected!'
and
'So, Im a very new Virus, under Development, so there will be much more functions when im finished.'
This hardly sounds like a legal use to me.
Likewise, DarkComet RAT’s author states “This software allow you to make hundreds of functions stealthly and remotely without any kind of autorisation in the remote process.” and references the term “Bot Shell” in his Mac OS X development build.
Some folks provided feedback that I had used the acronym RAT incorrectly, saying it stands for Remote Access Tool, not Remote Access Trojan. While the authors would like you to believe they are simply tools, I think the evidence suggests Trojan is more appropriate.
If you are interested in what you can do to protect your Mac, check out Ben Jupp’s Mac OS X security tips part 1, part 2 and part 3 and download our free Sophos Anti-Virus for Mac Home Edition.
Creative Commons image of Rat Fink courtesy of Jennifer Ennis’s Flickr photostream.
MacSpy is advertised as the 'most sophisticated Mac spyware ever”, with the low starting price of free. While the idea of malware-as-a-service (MaaS) isn’t a new one with players such as Tox and Shark the game, it can be said that MacSpy is one of the first seen for the OS X platform.
The authors state that they created this malware due to Apple products gaining popularity in the recent years. They also state that during their tenure in the field that they have noticed a lack of 'sophisticated malware for Mac users' and they believe that 'people were in need of such programs on MacOS'. So they created MacSpy. The MacSpy authors claim to have the following features in the free version of their RAT:
If you are willing to pay an unknown amount of bitcoins for the advanced version, the malware authors advertise the following features:
MacSpy is not as polished as some of the malware-as-a-service providers out there, as there doesn’t seem to be any customer facing automated service of signing up for their service. In order to receive a copy of MacSpy we had to email the author our preferred username and password, in order for them to make us an account. After confirming our details they created an account for us, and delivered a zipped file and the following instructions:
Initial Analysis
After unzipping the archive we observed it contained the following files:
The archive contains four files:
- Mach-O 64-bit executable called 'updated'
- Mach-O 64-bit executable called 'webkitproxy'
- Mach-O 64-bit dynamically linked shared library called 'libevent-2.0.5.dylib'
- Config file
After examining webkitproxy and libevent-2.0.5.dylib, we noted they are signed by Tor, and thus we concluded that they are related to the function of Tor Onion routing. The contents of the config file further convince us of our suspicions are correct:
Config Contents
The 'updated' file, on the other hand is not digitally signed, and it is currently completely undetected by various AV companies on VirusTotal.
Anti-Analysis
MacSpy has several countermeasures that hamper analysis efforts. To prevent debugging, it calls ptrace() with the PT_DENY_ATTACH option. This is a common anti-debugger check and will prevent debuggers from attaching to the process.
If you bypass the ptrace countermeasure, MacSpy has additional code that checks if it is running in a debugger.
The code above is very similar to the debugger checking code from this Stack Overflow post.
In addition to the anti-debugging countermeasures, MacSpy contains checks against the execution environment that can make it difficult to run in a virtual machine. In the code below, you can see that MacSpy checks that the number of physical CPUs is greater than 1, the number of logical cores is greater than 3, and the number of logical cores is twice the number of physical cores. MacSpy also checks that there is at least 4 GB of memory on the host. Since malware sandboxes often run with minimal resources, these checks can prevent proper execution in virtual environments.
Similar to MacRansom, MacSpy also compares the machine model to 'Mac' using the 'sysctl' command. MacSpy will kill all Terminal windows which can be annoying to analysts using command line tools to analyze the malware (OSX/Dok exhibits similar behavior by killing Terminal windows).
Persistence
In order to persist on the system the malware creates a launch entry in ~/Library/LaunchAgents/com.apple.webkit.plist. This ensures that the malware will run at start up to continue collecting information. Wmv codec for mac.
Behavior Analysis:
Upon execution, successfully passing the anti-analysis checks and setting persistence, the malware then copies itself and associated files from the original point of execution to '~/Library/.DS_Stores/' and deletes the original files in an attempt to stay hidden from the user. The malware then checks the functionality of its tor proxy by utilizing the curl command to contact the command and control server. After connecting to the CnC, the malware sends the data it had collected earlier, such as system information, by sending POST requests through the TOR proxy. This process repeats again for the various data the malware has collected. After exfiltration of the data, the malware deletes the temporary files containing the data it sent.
The following curl command used to exfiltrate data:
Contents of ~/Library/.DS_Stores/data/tmp/SystemInfo
User Web Portal
In our initial email to the malware authors we sent a set of credentials that we wanted to use in their web portal. After logging into the MacSpy web portal you are greeted with a very bare bones directory listing containing a folder labeled the most recent date of the malware executing on a system in the YYYYMM format, followed by a folder in the DD format. Diving into that folder you're treated with a series of directories similar to that of the directory naming on the victim system. Inside these folders is the data that was collected from the victim the malware was executed on.
Detection
NIDS
Rat Mac Os X
The best way to detect MacSpy running on a Mac is to use a combination of Network IDS (NIDS) rules as it communicates. As it turns out, AlienVault provides this rule in its threat intelligence, which has already been updated with a rule called 'System Compromise, Malware RAT, MacSpy'. This feeds into the USM correlation engine to generate an alarm that will notify AlienVault customers that one of their systems is compromised.
Rat For Mac Os X 10.7
Osquery
Yara
You can use the rule below in any system that supports Yara to detect this Mac-based malware.
Conclusion
Rat For Mac Os X 10.8
People generally assume when they are using Macs they are relatively safe from malware. This has been a generally true statement, but this belief is becoming less and less true by the day, as evidenced by the increasing diversity in mac malware along with this name family. While this piece of Mac malware may not be the most stealthy program, it is feature rich and it goes to show that as OS X continues to grow in market share and we can expect malware authors to invest greater amounts of time in producing malware for this platform.
Rat For Mac Os X 10.10
If you want to find out more about this malware, here is a pulse we have in the AlienVault Open Threat Exchange (OTX):
Appendix:
6c03e4a9bcb9afaedb7451a33c214ae4
c72de549a1e72cfff928e8d2591d7e97
cc07ab42070922b760b6bf9f894d0290
27056cabd185e939195d1aaa2aa1030f
f38977a34b1f6d8592fa17fafdb76c59